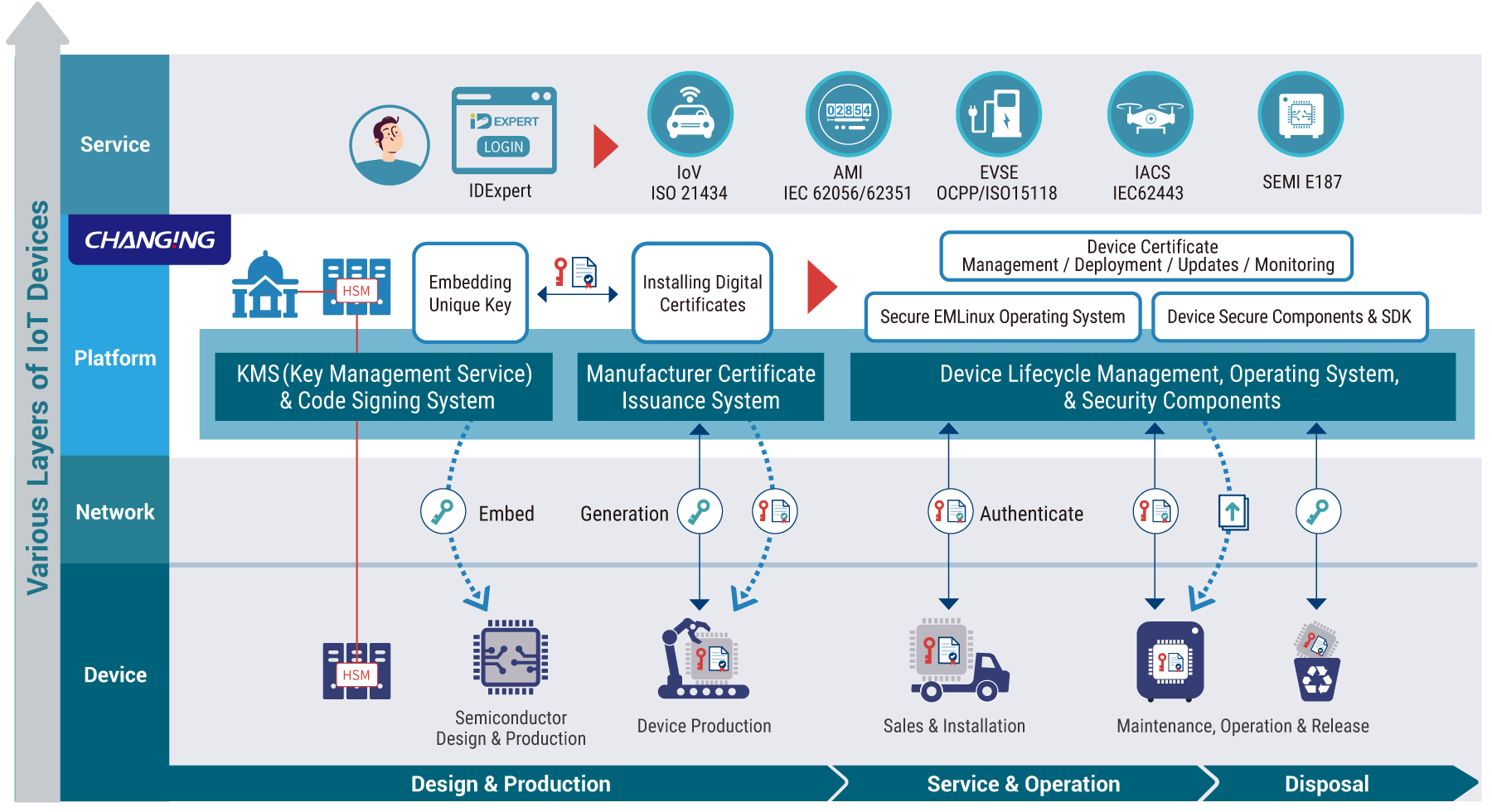
End-to-End IoT Security Across the Entire Lifecycle
 Hardware-Based Protection to Strengthen Security at the Core
Hardware-Based Protection to Strengthen Security at the Core
Reinforces security at the hardware level to prevent key leakage and identity spoofing, while enhancing device level defenses and minimizing potential vulnerabilities.
 Integrated Software Solutions for Streamlined Security Management
Integrated Software Solutions for Streamlined Security Management
Secure and reliable management of software certificates and encryption keys at every stage, from chip design and manufacturing to deployment and ongoing device operation.