More Than an HSM, CHANGING BringsYou a Complete Interoperable Security Solution.

Keys Are Generated & Stored Inside Secure Hardware
HSM isolates key generation, storage, and usage within secure hardware.
Signing and verification are executed internally, preventing key exposure.
Supports secure boot, OTA pre-verification,& API-based signing.
KMS Centralizes Key Management & Access Control
Unified key issuance, rotation, and traceability under Ciot KMS.
Consistent policies applied across factories and services.
MES (Manufacturing Execution System) and DevOps integration streamlines automation and reduces errors.

Automated Signing for CI/CD from Verification to Updates
HSM anchors code signing and OTA update processes.
Combined with Ciot KMS, enables end-to-end CI/CD automation.
Ensures traceability, compliance, and alignment with DevSecOps.
High-Availability HSM Cluster for Peak Load Resilience
Clustered HSMs balance load and synchronize data, with health checks that trigger automatic failover. Key policies remain consistent across nodes to keep services running during maintenance or incidents.
Centralized Key Inventory with Rapid Recovery
Integrates with provisioning and secure enrollment so keys are added together with device certificates and firmware details. Smart-card or token backups allow quick cross-site restoration using standard formats.

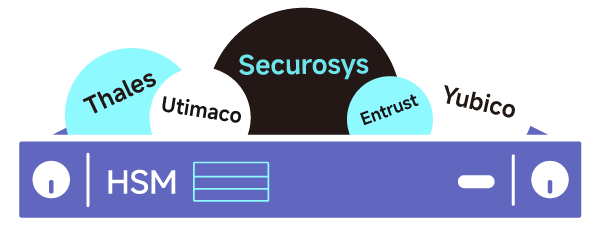
Multi-Vendor HSM Support for Diverse Systems & Scalability
Compatible with Securosys, Thales, Utimaco, Entrust, and Yubico, the architecture adapts to different scales and environments. It supports smooth expansion while keeping resources well balanced.