CodeSign × Secure Boot × Root of Trust
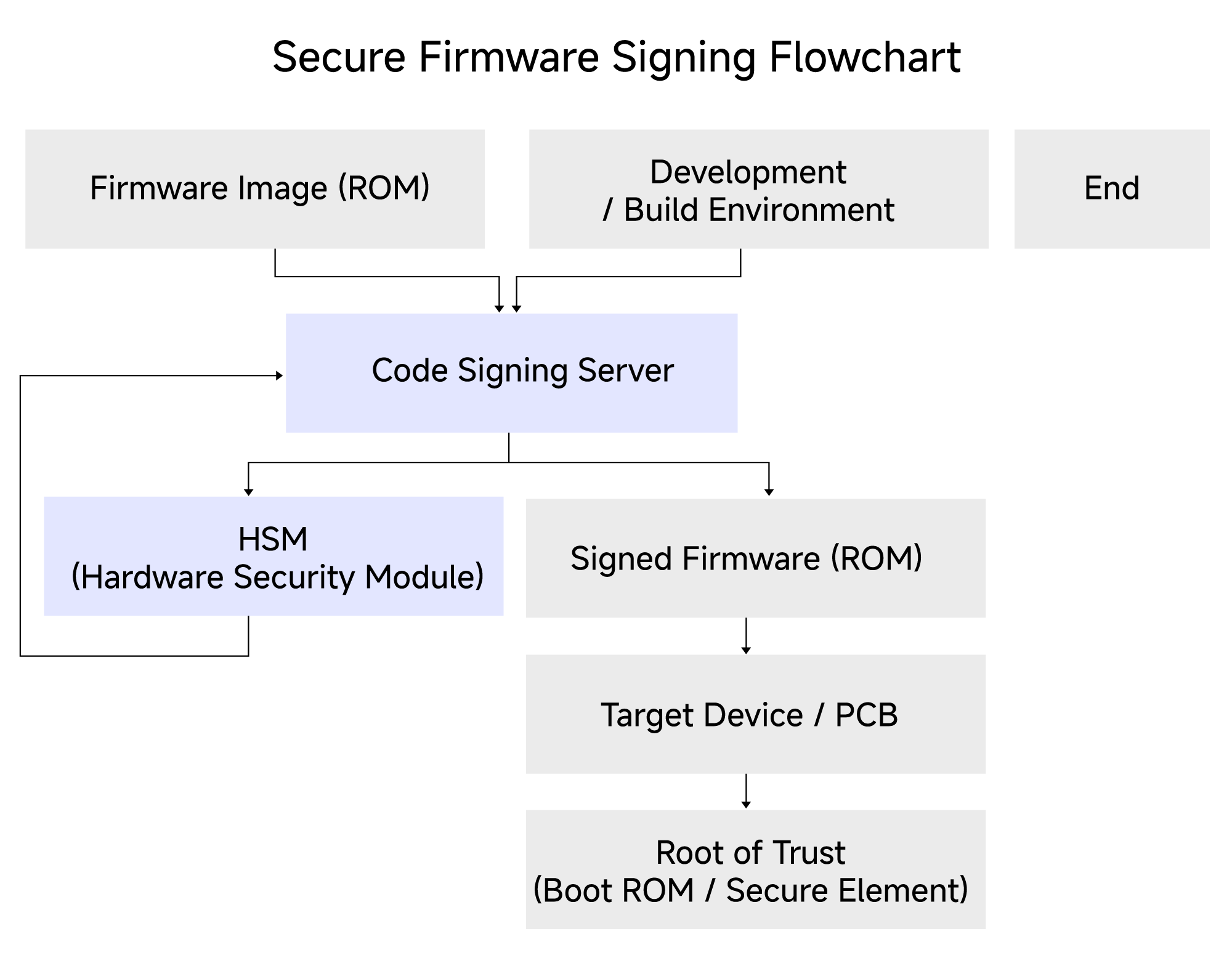
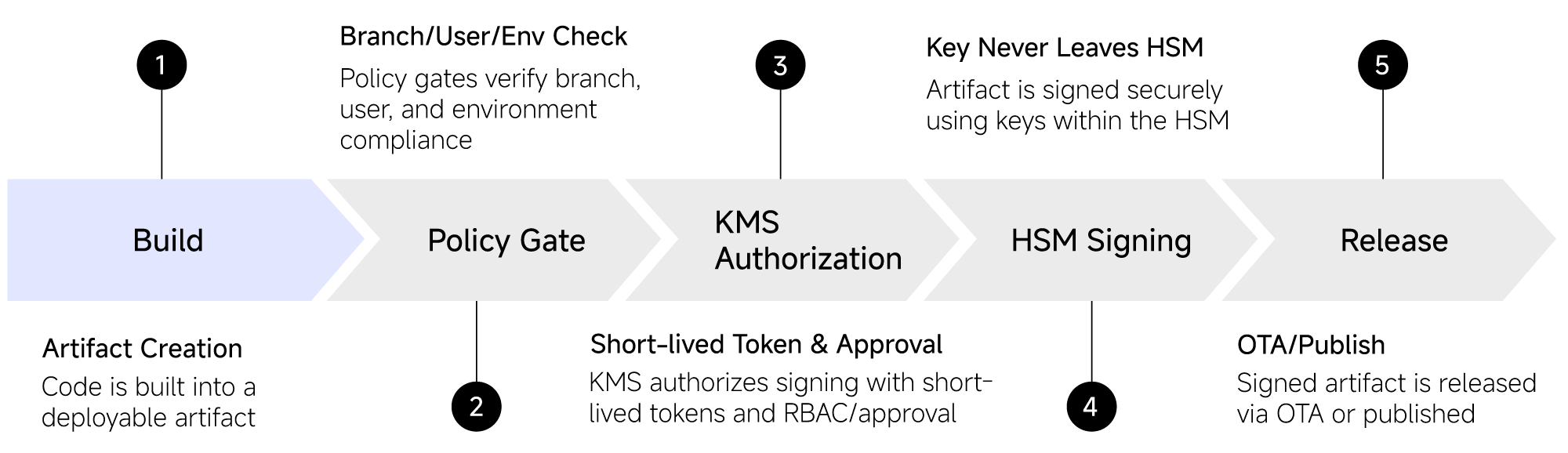
Building a complete trust chain starting from the hardware (Chain of Trust), with each verification step relying on rigorously signed software images.
CHANGING assists clients in establishing a software trust foundation on MCUs, SoCs, and endpoint devices that can be validated and managed over the long term. During device boot, code is verified layer by layer starting from the Root of Trust (e.g., Boot ROM). Without a governable Code Signing mechanism, Secure Boot cannot be fully enforced.