

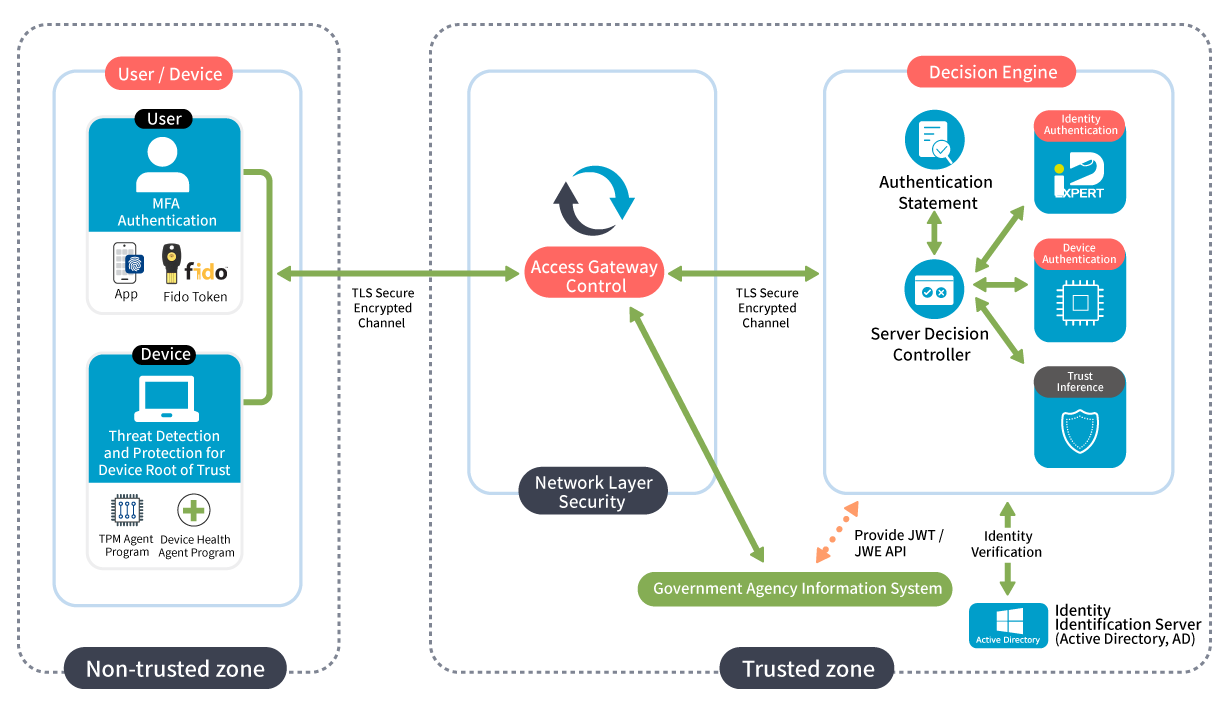
Network Control: Alllow or restrict network segments based on trust levels, or directly permits access using a Reverse Proxy.
Authentication Statement: Use strong authentication methods like FIDO2 for identity verification. Check if the device's TPM has a registered device certificate.

Zero Trust Architecture is based on the concept of "never trust, always verify," requiring repeated and multifaceted verification to establish trust before accessing data. Its three core mechanisms are:
Identity Authentication: Multi-factor authentication and identity assertions.
Device Authentication: Device authentication and device health management.
Trust Inference: User context trust inference mechanisms.
Zero Trust Network Architecture focuses on protecting resource access:
Emphasize protecting data and application access over perimeter defense.
Lack specific boundaries; users, devices, data, and applications are in different network environments.
Never trust any data access request and continuously verify.


Taiwan government is promoting the Zero Trust Network Architecture, focusing on top-tier public agencies responsible for information security like the Presidential Office, Executive Yuan, National Security Bureau, Ministry of National Defense, Ministry of Foreign Affairs, and the six metropolitan governments. This initiative aims to implement Zero Trust and develop a domestic cybersecurity industry chain.
2022 Identity Authentication 2023 Device Authentication 2024 Trust Inference
The first line of defense for all network services is ensuring identity security, a key aspect of Zero Trust. CHANGING's FIDO and OATH certified solution uses diverse verification mechanisms for various applications and integration services. This enables effective identity verification across industries and government agencies, enhancing information security. It improves network defense depth and breadth, achieving high-level security through proactive defense mechanisms, safeguarding enterprise gateways.

CHANGING's device authentication solution uses TPM hardware chip keys to establish device identity. Access to applications and enterprise resources is granted only after verifying the device's authenticity.

CHANGING's trust inference solution evaluates device health (OS updates, antivirus status, EDR, GCB/FCB compliance) and connection details (IP, location, time). Devices must meet health requirements to access resources; otherwise, connections are blocked in real time.
When users or devices need to access organizational resources, they must pass through a Policy Enforcement Point (PEP), with access rights determined by the corresponding Policy Decision Point (PDP).
After identity login, an authentication assertion must be obtained for verification and access approval.
Government Information Systems
In the Zero Trust Architecture, strong authentication must be performed before login, followed by a second phase login.
Windows/Linux/Mac Operating Systems
VPN Remote Access
VDI Remote Office Connections
Web Services
Email Systems


Implementing Zero Trust is a gradual, continually improving process. CHANGING assists organizations advance across the five pillars and three functional aspects of Zero Trust.
In the rapidly evolving enterprise environment and technological landscape, ZTMM offers a method for continuously modernizing Zero Trust operations. It covers the implementation gradients of the five pillars: Identity, Device, Network, Application, and Data. This allows for the gradual optimization and improvement of Zero Trust. Each pillar includes three horizontal functions: Visibility and Analytics, Automation and Orchestration, and Governance.

Citizen Digtial Certificate

CyCraft Technology
CloudFlare
Fortinet

Microsoft

F5