Identity Platform for Critical Workflows
Make Every Login Trusted
- Passwordless
- Zero Trust Auth
- FIDO2 Certified
- MFA


With the help of mobile device carriers, users can log in through facial or fingerprint recognition, without the need to remember any alphanumeric characters. Through unique biometric identification, the security of login authentication is made more convenient, fast, and secure, with the user themselves being the best defense factor.
IDExpert server is also a FIDO Server, allowing users to directly register FIDO devices. Through the SAML protocol, enterprise web pages and cloud services can perform FIDO authentication in the IDExpert SSO Portal.
FIDO UAF with mobile push authentication is supported, enabling passwordless authentication through IDExpert. FIDO2, which is used for web login, is also applicable. FIDO2 devices such as mobile phones, Bluetooth, and USB can be used as authentication carriers for multi-factor authentication.
To facilitate application system integration for large enterprises such as finance, IDExpert provides the FIDO SDK.
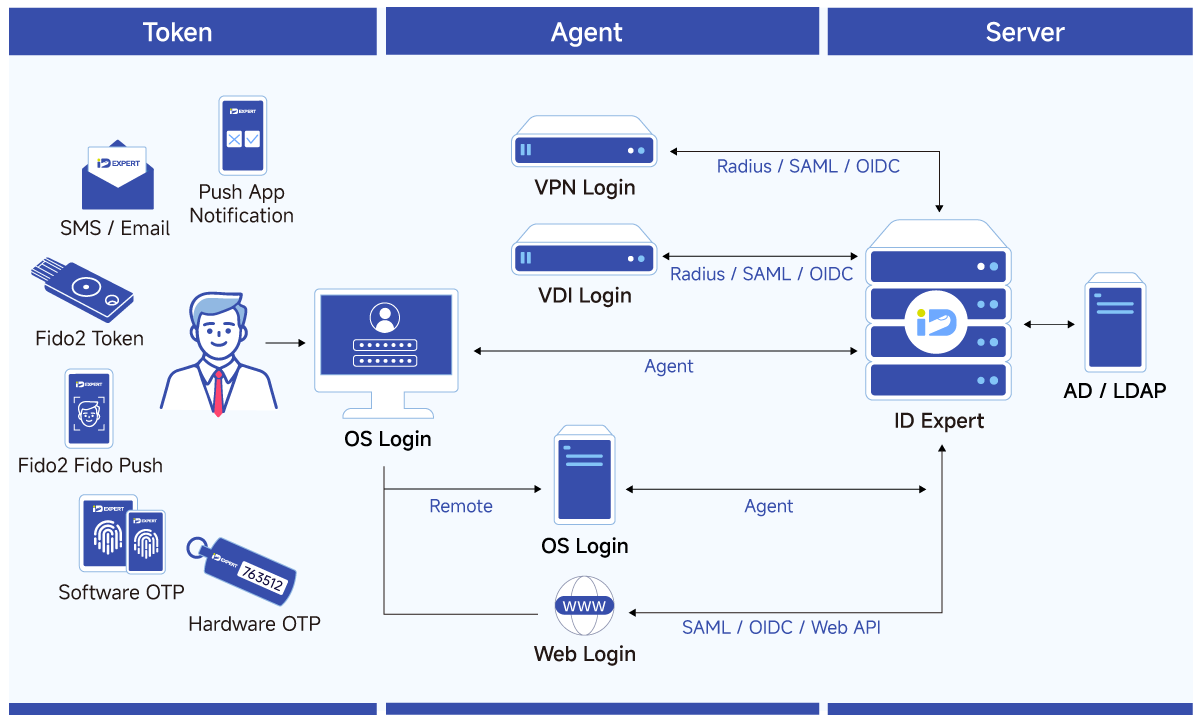
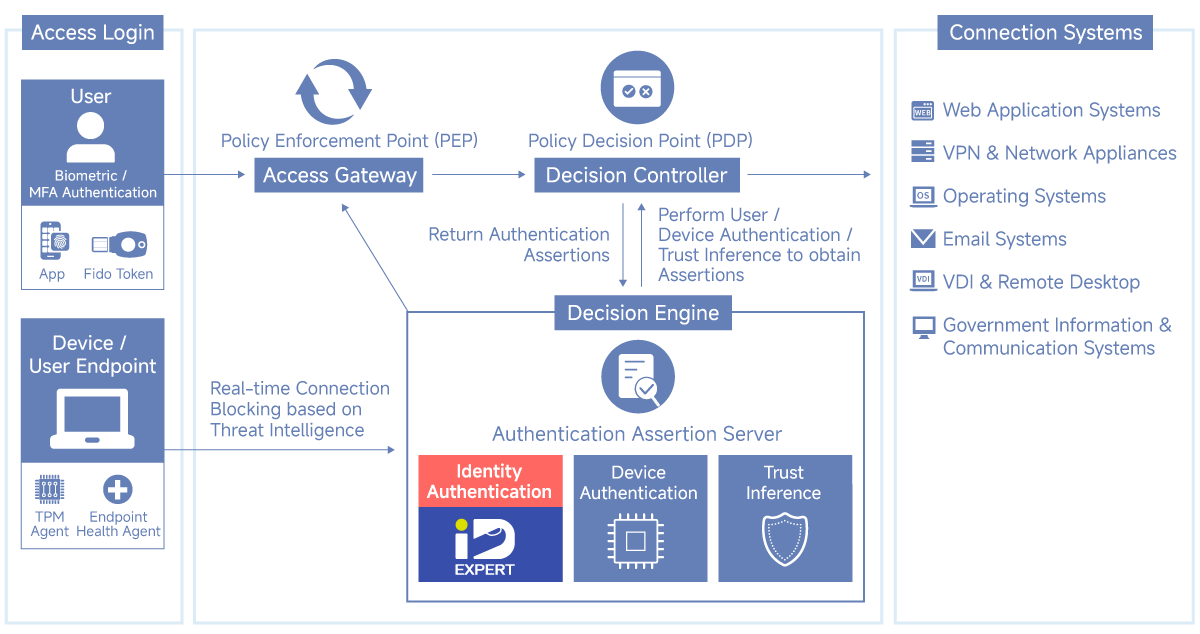
Seamless Zero Trust Expansion & Integration
When logging in to the application system, IDExpert can be used to perform FIDO biometric authentication to verify identity. Once registered, it can be used universally for operating systems, network devices, web pages, and more.
FIDO UAF combined with app push authentication no longer requires separate system integration, and the authentication devices used do not need to be registered separately, simplifying the traditional FIDO UAF integration process.
Define precise authentication rules based on risk and context.
Supports AD/LDAP, OTP, Push, FIDO2, and custom multi-channel On-Demand OTP.
Use Geofencing as a filter in auth paths to strengthen compliance and security.
Standard APIs allow developers to seamlessly embed authentication into existing workflows.
Fully compatible with OIDC and SAML, ensuring interoperability with modern ID systems.
Multi-device OTP support ensures account security through dynamic code generation.
Flexible binding: Each account supports up to 3 authentication devices.







Supports diverse heterogeneous systems, ensuring secure authentication across hybrid environments.
Direct access to local technical teams for customized workflows and rapid deployment.
Modular design that scales with business needs, supporting identity verification from on-prem to cloud.
Trusted by finance, government, and manufacturing. With deep experience in Office 365, AWS, VPN, and VDI, IDExpert helps IT architects deploy high-authority authentication services.
| Connection System | Application | Supported Firm |
|---|---|---|
| Networking System | VPN, Firewall, UTM, NAC, NOC |
                          |
| Server Management Sysytem | PAM, SWIFT, KVM |
        |
| Mail Server System | Outlook Web Access, Active Sync, IBM Notes |
    |
| Virtual Platform Management | VM PlatForm |
    |
| Virtual Desktop System | VDI |
     |
| Operating System | Windows, Linux |
    |
| Storage System | NAS, Storage |
     |
| Project Management System | Redmine, GitLab |
  |
| Enterprise Resource Planning | CRM, ERP, HRM |
   |
| Website Custimization | IIS, JAVA Filter, Restful API |
       |
| Single Sign On / Cloud service | SAML |
        |
Note: contact us for any other integration needs not listed above.
Serving high-compliance sectors with proven deployment expertise and regulatory best practices.
Adopted in e-government services, helping critical infrastructure build stable and compliant identity frameworks.
Long-term partner for financial groups, ensuring non-repudiation in digital banking and internal systems.
Providing flexible identity mechanisms for large-scale factories and global identity governance.
Leading the market with significant adoption in government and financial sectors. We leverage deep field experience to provide robust security for every client.