CHANGING Achieves Complete Three-Stage Government Zero Trust Architecture Verification
2026-03-13
Identity Authentication, Device Authentication, and Trust Inference — All Three Stages Among the First Wave Certified by Taiwan’s National Institute of Cybersecurity (NICS)
CHANGING (a Wistron Group company) announced the successful completion of the National Institute of Cybersecurity’s (NICS) conformance verification for Taiwan’s Government Zero Trust Architecture, covering Identity Authentication, Device Authentication, and Trust Inference — becoming one of the first vendors to pass the third-stage “Trust Inference” verification. With this achievement, CHANGING has now received official NICS certification across all three core mechanisms, and has been among the first wave of vendors certified at every single stage, setting the highest benchmark in Taiwan’s zero trust cybersecurity industry.
Under Taiwan’s Executive Yuan “6th National Cybersecurity Development Plan (2021–2024)”, the government’s Zero Trust Architecture rollout prioritizes Class-A cybersecurity-responsible agencies — including those handling national classified information, diplomacy, national defense, nationwide shared IT systems, and public medical centers. Verification proceeds in three sequential phases: Stage 1 “Identity Authentication”, Stage 2 “Device Authentication”, and Stage 3 “Trust Inference”, which together form the complete closed-loop decision engine of the Zero Trust Architecture.
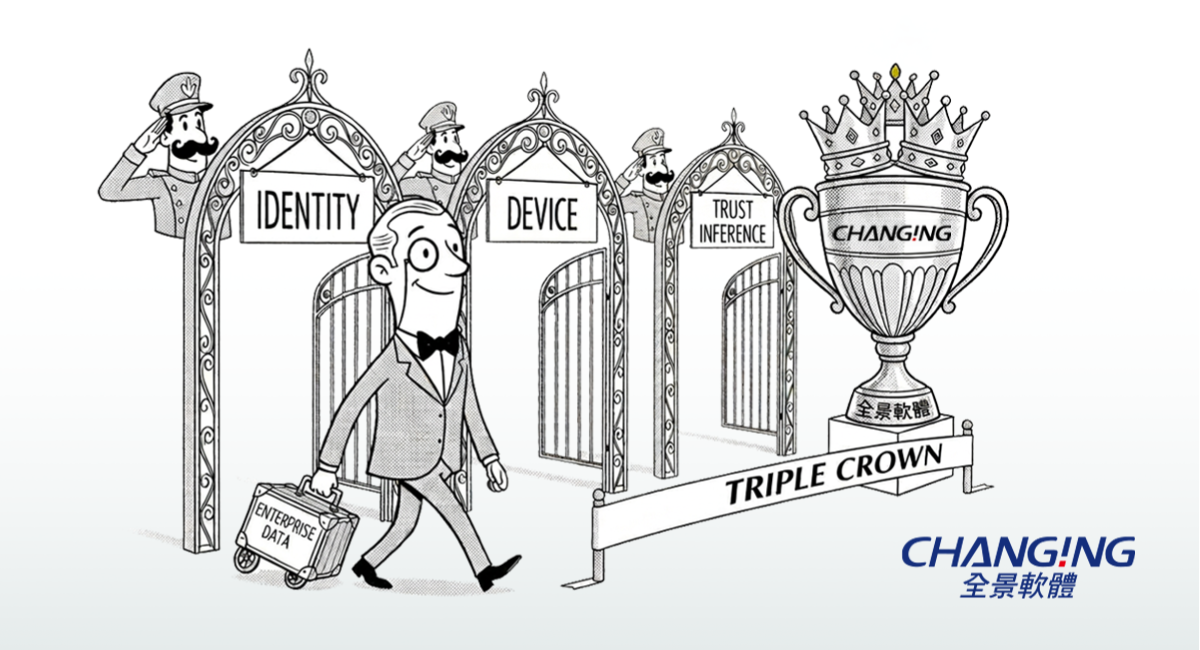
image: Three gates cleared, triple crown earned - CHANGING becomes the first vendor to complete all three stages of Taiwan's government Zero Trust Architecture certification.
CHANGING committed to verification from the very outset of the government’s Zero Trust initiative, earning first-wave certification in both Stage 1 and Stage 2. Now completing Stage 3 with the same first-wave status, the company has achieved what the industry calls a“Triple Crown” — a historic milestone. Among domestic vendors offering full three-stage verification with first-wave status at every stage, CHANGING stands as the most representative choice in the market.
Trust Inference is the most technically complex of the three mechanisms. Compliant with NIST SP 800-207, it integrates multiple inference factors — OS version, antivirus status, device health level, threat intelligence feeds, and more — each assigned a configurable weight for dynamic scoring. The decision engine evaluates these signals in real time to grant or revoke resource access. Unlike static login-time authentication, Trust Inference provides continuous, dynamic risk assessment: even if a legitimate account is compromised, anomalous behavior immediately triggers privilege downgrade or session termination, effectively containing lateral movement within the network.
For Device Authentication, CGTrust leverages the TPM (Trusted Platform Module) security chip to establish device uniqueness;any device not pre-registered and approved via TPM cannot even reach the identity authentication step, forming a hard perimeter at the very first point of access. All of Changingtec’s Zero Trust products are developed entirely in-house with no dependency on foreign vendor licenses, offering government agencies the highest assurance of technological sovereignty and supply-chain security.
“Zero Trust is not a slogan — it demands real, verified technical capability. CHANGING has been deeply rooted in identity authentication for over 26 years. Being among the first wave certified at every critical stage of the Government Zero Trust Architecture is the best proof of our long-term technology investments. We are committed to being the most trusted zero trust partner for government agencies, and to building a resilient digital foundation for Taiwan together.”
── Anderson Yang, General Manager, CHANGING Co., Ltd.
The CGTrust Zero Trust Solution uses a reverse-proxy gateway as the single point of access, supporting web applications, VPN, VDI, privileged systems, Windows/Linux/macOS operating systems, cloud services (OIDC/SAML), email systems, and storage systems —one unified platform governing all access entry points. The Identity Authentication module supports Changingtec’s own FIDO and MFA mechanisms as well as IC-based citizen digital certificates, mobile citizen digital certificates (TWFIDO), smart card credentials, and any mechanism meeting AAL3 or higher, flexibly adapting to each agency’s existing environment.
To date, CHANGING c has completed live deployments at over 30 government and financial institutions across Taiwan. All development and deployments are carried out by CHANGING’s own engineers — no outsourcing — enabling fast custom integration and responsive maintenance support.
CHANGING – Marketing & PR Department
Tel: +886-3-563-0688
EMAIL:marcom@changingtec.com
CHANGING Information Technology Inc.
Committed to independent research and development, CHANGING strives to build a secure and convenient digital environment. Its core expertise lies in identity and authentication security for people, processes, and devices, including zero trust architecture, IoT security, FinTech cybersecurity, and digital transformation applications. With more than 25 years of professional experience, CHANGING's mission is to help various industries establish a trustworthy and secure zero trust network infrastructure. Through continuous innovation, it provides diverse products and services to meet the evolving needs of customers, working together to create a safer and more efficient digital ecosystem. In the digital age, CHANGING aims to be your most trusted partner.