
Security Solution
Ciot provides complete IoT security from chip design to system integration. Smart certificate and key management protect digital identities and communications, enabling secure and trusted device connectivity.
Reinforces security at the hardware level to prevent key leakage and identity spoofing, while enhancing device level defenses and minimizing potential vulnerabilities.
Secure and reliable management of software certificates and encryption keys at every stage, from chip design and manufacturing to deployment and ongoing device operation.
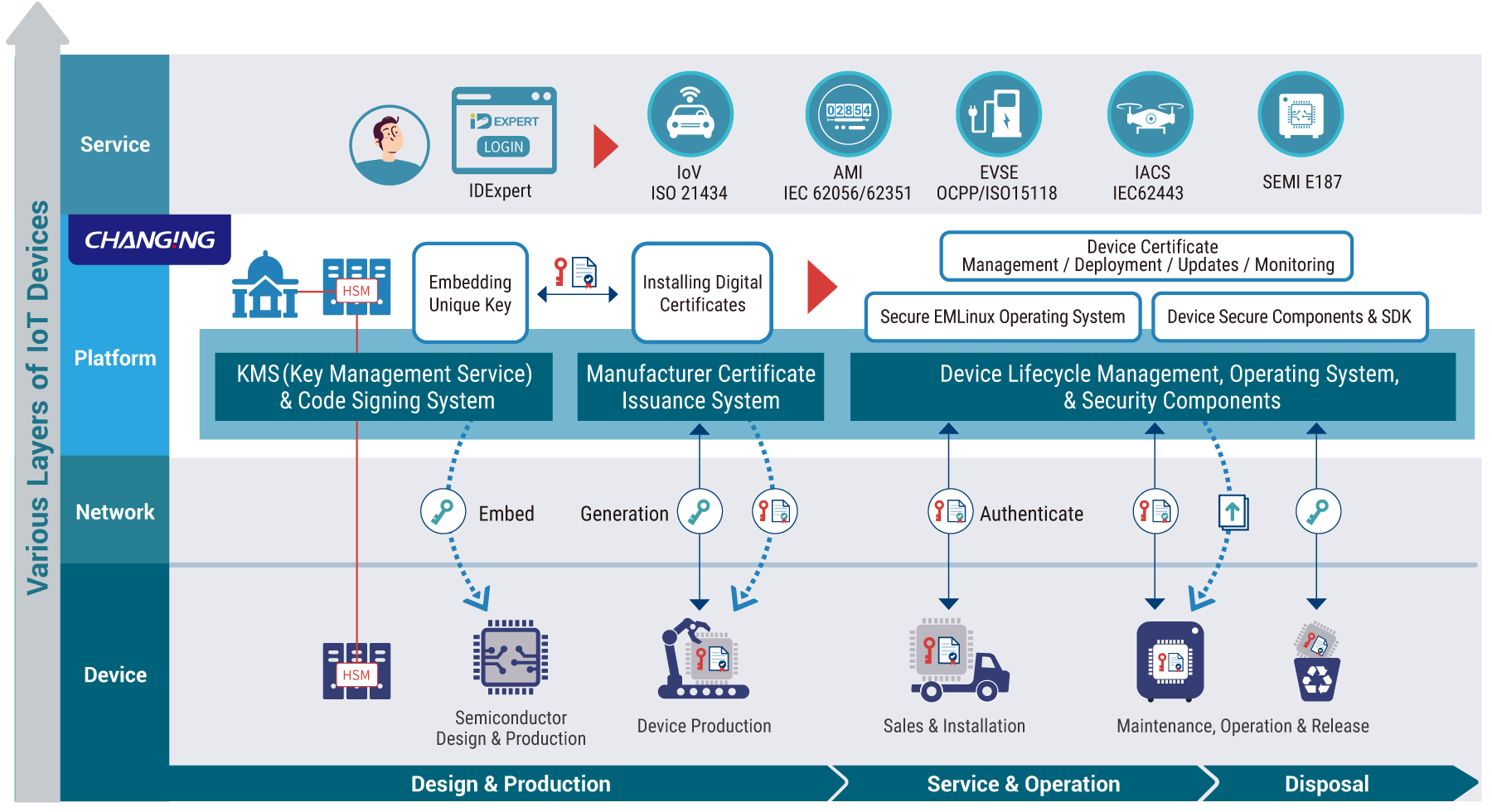
Use certificate-based identity to give each chip a verifiable identity from production. With RoT, hardware key protection, and secure provisioning, ensure full-process protection and defend against counterfeiting and data leaks.

Prevent disruptions with PKI-based authentication for sensors, controllers, and edge devices. Manage certificates and keys throughout the lifecycle to secure updates and maintain process integrity.

Ensure stable, secure operation of meters and sensors with certificate management, RoT design, signature validation, and key revocation. Meet global standards like IEC 62443 without service interruption.

Protect ECUs, chargers, and V2X endpoints with certificates, hardware-based keys, and update validation. Meet standards like ISO/SAE 21434 and secure the software supply chain with custom RoT and key management.

Secure manufacturing, updates, and connections with Matter-compliant certificates, digital signatures, and hardware key storage. Build trust and accelerate product launch from the design stage.
We bring proven digital ID expertise to IoT, helping businesses quickly establish trusted device identities and take control of security.
Full automation from issuance to renewal and revocation reduces errors, boosts efficiency, and ensures compliance.
Manage certificates and security tasks for multi-source devices in one platform, simplifying operations and risk control.
Easily expand from small setups to global deployments. Our platform adapts to diverse industries with reliable, future-ready security.
The rapid development of the Internet of Things (IoT) has brought brand new opportunities to various industries, while also introducing unprecedented challenges. As IoT devices play an increasingly important role in our daily lives and work, protecting these devices and the data they carry has become a critical task. To help you establish a secure and reliable IoT environment, we offer the following 5 security recommendations.

Each IoT device should possess a unique digital certificate to verify its identity and ensure data integrity. Traditional methods such as fixed passwords or shared keys are no longer sufficient to address the security challenges of IoT. Therefore, the importance of having a unique digital certificate cannot be overlooked.
These digital certificates can be provided by manufacturers or generated internally by enterprises and organizations. The certificate should include essential identity information about the device, such as the manufacturer, model, and serial number, to ensure accuracy and traceability.Using unique certificates offers the following benefits:
Verify the identity of the device
Ensure data integrity of the device
Prevent device spoofing or impersonation
Restrict access and control of the device

Private keys play a crucial role in IoT security, and storing them securely in hardware, such as a Trusted Platform Module (TPM) chip, provides a higher level of security.
If private keys are leaked, devices may be vulnerable to attacks and control. Therefore, storing private keys in hardware is essential. TPM chips, as secure encryption processors, can effectively prevent misuse of private keys.
TPM chips offer the following functions:
Securely store private keys
Perform encryption operations
Protect devices from attacks

IoT devices should strictly validate the digital signatures of firmware and software updates to ensure their authenticity and integrity. Digital signatures use cryptographic techniques to sign electronic files, ensuring that the data is not tampered with or altered during transmission.
By validating digital signatures, IoT devices can ensure the authenticity of firmware and software updates, preventing potential vulnerabilities or security risks introduced by unauthorized modifications. This measure effectively prevents malicious third parties from intervening and ensures the security and stability of system operations.
The benefits of validating digital signatures include:
Ensuring the authenticity of firmware and software updates
Preventing tampering or forgery of firmware and software updates
Protecting devices from malicious software attacks

Roots of trust (RoT) play a crucial role in IoT security, serving as the cornerstone for establishing a secure trust chain. The trust chain refers to a series of trust relationships extending from each device to the root of trust. By establishing organization-specific roots of trust, businesses and organizations can have complete control over all critical elements in the trust chain.
This approach allows businesses and organizations to independently determine which devices and personnel should be trusted and ensures that the entire system remains free from unauthorized interference or damage during operation. By establishing specific roots of trust, organizations can effectively build a robust and reliable security framework to address the security challenges in the increasingly complex IoT environment.

A Key Management System (KMS) is a crucial platform for key backup and recovery operations, working in conjunction with a certificate management system to store encryption keys and perform recovery tasks. This system can back up multiple keys simultaneously, providing a secure encryption environment for organizations and preventing the loss of keys that could result in the inability to recover important electronic documents.
In IoT devices, certificates and keys should have the properties of being updatable, replaceable, and revocable to ensure system security. Additionally, online operations can be used to manage operator permissions, key settings, certificate installations, and key backup and recovery records to ensure effective and secure management.
Updatability: As time passes, encryption algorithms may be compromised. Therefore, certificates and keys should be updatable to utilize stronger encryption technologies.
Replaceability: If certificates or keys are compromised, they should be replaceable with new ones.
Revocability: If certificates or keys are no longer secure, they should be revocable.