Introduction
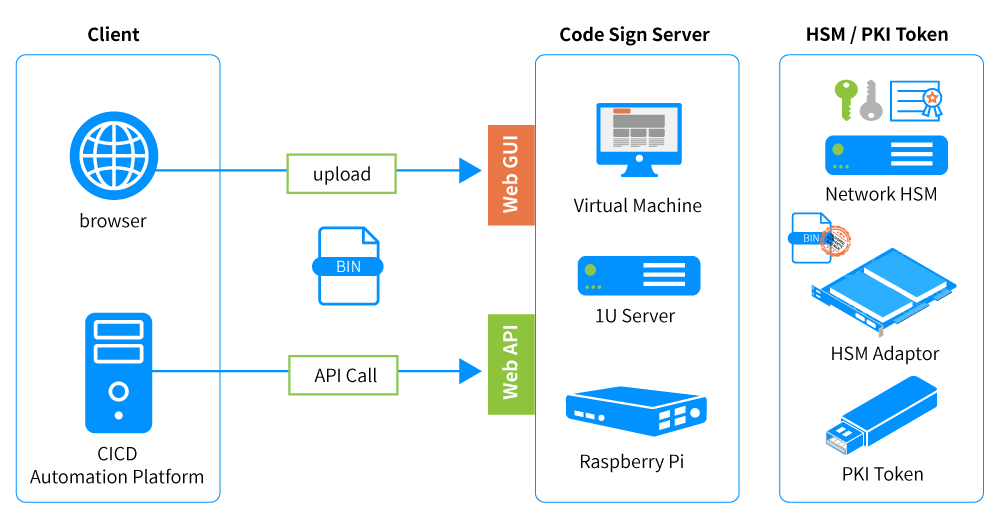
After completing code writing or compilation, commercial software and application developers can use PKI mechanisms and trusted third-party digital certificates to sign their software before distribution. This prevents unauthorized tampering or repackaging by unknown parties. When customers download or execute the program via the internet, the digital signature verifies the software's origin and integrity, ensuring it remains untampered.